Architecture
System Architecture
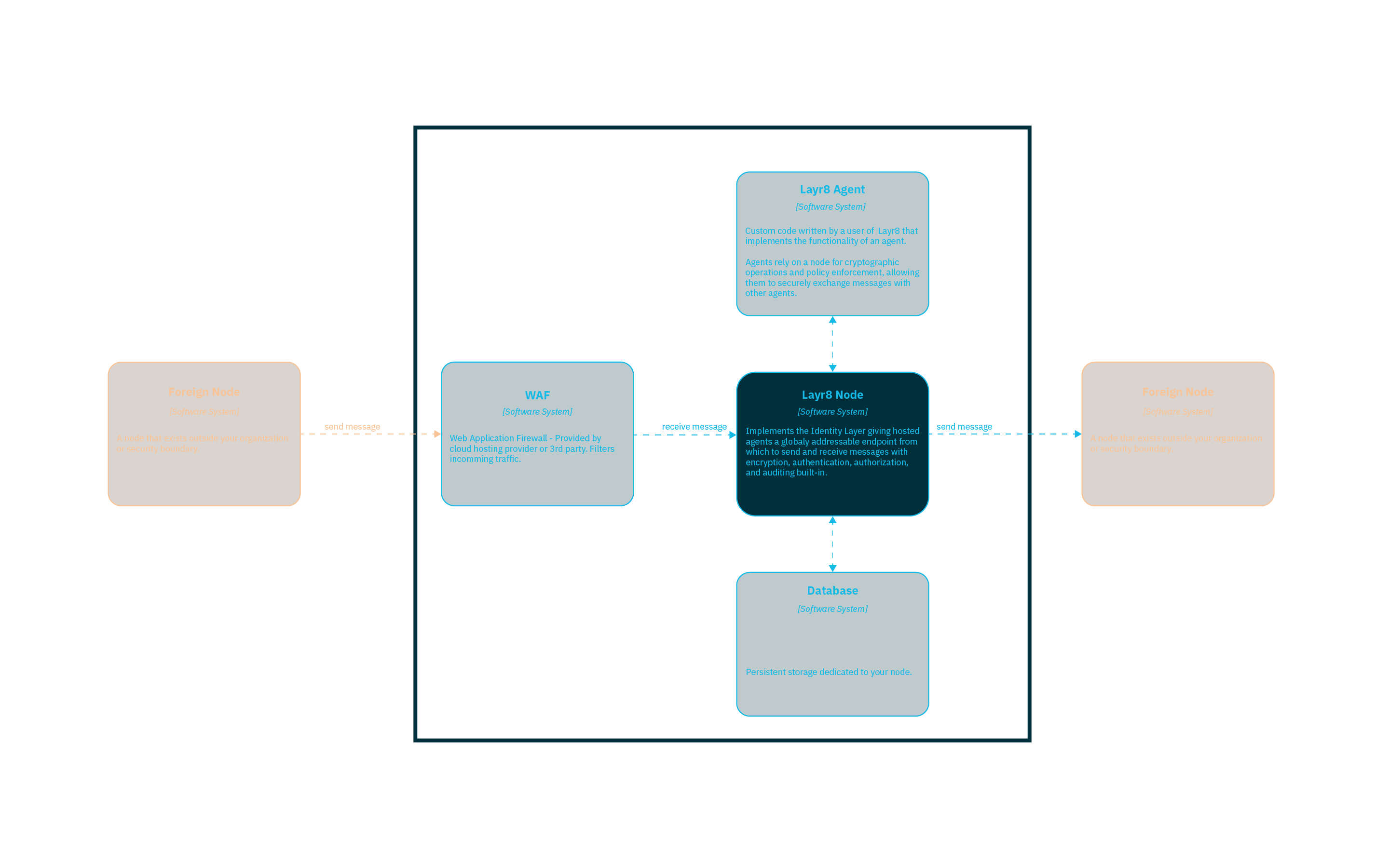
Understanding Layr8’s architecture helps you plan deployments, reason about security boundaries, and integrate with existing infrastructure. This page provides a high-level view of how a Layr8 Node fits into your environment and communicates with the broader network. For conceptual background on Layer 8 and decentralized identity, see What Is Layer 8?.
This diagram shows the high-level system context architecture of a Layr8 Node. It shows your node at the center with other key systems it interacts with.
Components
Your Security Boundary
The blue bordered area represents your organization’s security boundary. Everything within this boundary is under your control and is not accessible to other organizations.
Layr8 Agent
Custom application(s) written by you that implement your business logic. Agents can send and receive messages to any other agent on the network securely using Layr8.
Layr8 Node
The core software system that hosts your agents and provides the cryptography, policy enforcement, auditing and messaging infrastructure your agents need to communicate securely with other agents.
WAF (Web Application Firewall)
Provides an additional layer of security by filtering incoming traffic before it reaches the Layr8 Node.
Database
PostgreSQL database that stores all persistent node state:
- Private keys — Encrypted at rest using AES-256-GCM. Keys are decrypted into a secure in-memory store at runtime and never exposed in plaintext on disk.
- DID records — Hosted DIDs and their metadata, bookmarked external DIDs, and peer DID relationships.
- Verifiable credentials — Both issued credentials and holder credentials presented during authorization.
- Messages — Queued DIDComm messages for offline agents, with expiration.
- Authorization policies — Allow/deny lists and credential status lists for revocation.
- Protocol state — Conversation thread state for multi-step DIDComm protocols.
- Node configuration — API keys, user accounts, and egress quota tracking. API keys are used only within your security boundary to authenticate agents to the node — they never cross organizational boundaries.
Foreign Node
External Layr8 Node (or other DIDComm-compatible server) that your Layr8 Node communicates with. Foreign nodes rely on the same standards but are owned or operated by other organizations outside of your security perimeter.
Message Flow
- Outbound: Your Agent sends a message through the Layr8 Node, which routes it through the network to the recipient’s DIDComm server.
- Inbound: Foreign DIDComm servers send messages to your Node for delivery to your Agent.
All messages are packed with authenticated encryption (ECDH-1PU). The sender’s identity is proven during decryption — only someone with the corresponding private key could have produced the message. Before delivering an inbound message to your agent, the node enforces authorization policies: per-DID allow/deny lists, grant checks, and verifiable credential validation. Both nodes record every interaction in hash-linked audit chains — tamper-evident, independently verifiable by both parties.

